최고의 DMCA 테이크다운 서비스로 OnlyFans 콘텐츠를 유출로부터 보호하십시오.빠르고, 신뢰할 수 있으며, 익명으로 현재 소득을 보호할 수 있습니다.
역이미지 검색을 사용하여 포르노 사진이 유출되었는지 확인하십시오
목차
당신의 포르노나 사적인 사진이 유출되었는지 확인하고 어디서 재사용되고 있는지 알아내라.
당신의 포르노나 사적인 사진들이 온라인에 유포될까봐 걱정하기 시작하면, 가장 어려운 부분은 확인이 아니라 바로 확인이다그들이 어디서 끝이 났는지, 얼마나 멀리 퍼졌는지도 모른다.
아마도 그 사진들은 데이트 상대와 공유되었을 것이다.
어쩌면 당신이 크리에이터인데 유료 콘텐츠가 낯선 사람에게 갑자기 너무 친숙하게 느껴질 수도 있다.
어느 쪽이든 우려는 같습니다:내 이미지들이 이미 나와 있는가-만약 그렇다면, 누가 그 이미지들을 사용하고 있고, 어디서 사용하고 있는가?
리버스 이미지 검색은 일반적으로 첫 번째 단계입니다.
하지만 진짜 답을 원한다면, 추측법이 아닌 의도를 가지고 이루어져야 한다.
🔧 反 向 搜 索
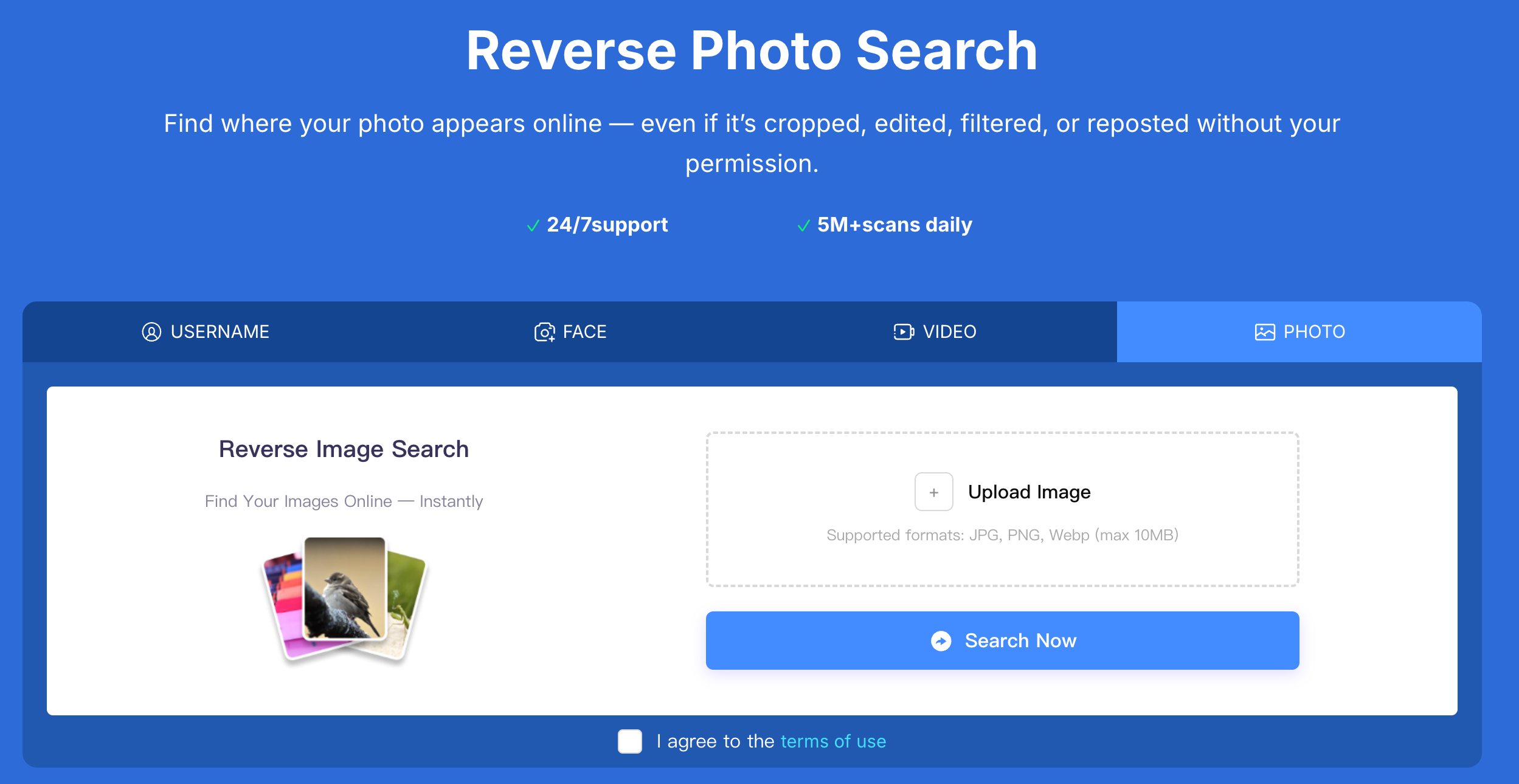
✅ 에라사에서 리버스 이미지 검색을 사용하여 비공개 사진이 유출되었는지 확인합니다
음란물이나 비공개 사진 유출을 적극적으로 추적하는 방법은 무엇일까
대부분의 사람들은 리버스 이미지 검색을 한 번 확인하는 것으로 취급합니다:
이미지를 업로드하고, 몇 가지 결과를 훑어보고, 최상의 결과를 바랍니다.
그 접근법은 거의 항상 계속되는 오용을 놓친다.
새는 것은 한 곳에 머물지 않는다.
그들은 다른 아이디로 재게시되고, 이름을 바꾸고, 번들로 팔리고, 재사용됩니다.
그렇기 때문에 실제 정보 유출을 다루는 사람들-특히 창작자들-과 같은 구조화된 역검색 시스템에 의존한다Erasa .
"결과 찾아보기"가 아니라 다음을 수행합니다 자신의 원본 콘텐츠가 어디서 어떻게 허가 없이 사용되고 있는지 추적합니다.
차이점은 간단합니다:
한 가지 접근법이 성냥을 찾는다;
다른 하나는 오용의 양상.
보통 음란물 유출이 시작되는 현실 세계의 두 시나리오
사적인 관계가 끝난 후에
이것이 가장 흔한 계기 중 하나입니다.
사진은 비공개로 공유되었습니다.
그들은 결코 공적으로 될 수 없었다.
낯선 메시지, 복사된 이미지 또는 인식하지 못하는 계정 등 이상한 느낌이 듭니다.
이러한 경우, 유출은 종종:
- 처음엔 조용했지만
- 작은 동그라미로 나누다
- 점차 공개 사이트에 다시 게시되었습니다
대부분의 사람들이 확인할 때 쯤에는 이미 이미지가 이동했습니다.
유료 성인 콘텐츠가 재게시되거나 재판매될 때
창작자들에게 유출은 한 장의 도둑맞은 게시물처럼 보이는 경우는 거의 없다.
대신, 내용은 다음과 같을 수 있습니다:
- 포르노 사이트에 재업로드되었습니다
- 재 포장으로 컬 렉 션"또는"번들
- 를 실행하는 데 사용 되는 흉내 계정
- 다양 한 사용자 이름 아래에서 되팔
이미지은 동일 한 맥락-변화 남아 있습니다.
포르노 또는 개인 사진 유출 어디 보통 결국
실제 추적 패턴을 기반으로 유출된 이미지는 가장 자주에 나타납니다:
- 성인 웹 사이트 검색 트래픽를 위해 만들어 집계는 콘 텐 츠
- 흉내 하거나 동일 한 사진을 사용 하여 거울 계정
- Grey-market 포럼 및 개인 커뮤니티
- 다운로드"콘 텐 츠 팩"판매를 파일로
- 크로스 플랫폼 재 게시 네트워크
이런 장소들 중 많은 사람들이 당신이 보통 방문 사이트 없다-는 왜 그렇게 오랫동안 눈에 띄지 않는 경우 가 많 샌다.어떻게 역 이미지 검색 (당신이 실제로 대답을 원하 다면) 끝내야 해
당신이 걱정하는 정확한 이미지를 사용하세요
잘리거나 흐릿하거나 편집된 버전을 피하십시오.
누수 종종 크기 조정을 포함 하거나 워터 마크 제거-원래 이미지을 통해 가장 강력 한 신호다.
단일 검색 엔진에 의존 하지 마
다른 플랫폼은 인터넷의 다른 부분을 색인화합니다.
한 장소에서 아무것도 찾을 의미 하지는 않는다 다른 곳에서 이미지 나돌고 있지 않다.
이미지 자체 너머로 본
사진을 얻 재사용-하지만 그러니까:
- 얼굴
- 사용자 이름
- 게시 패턴
치료하는 효과적인 추적 연결이 러한 신호를 대신 각 이미 지를 고립 된 사건으로 합니다.
원래 포르노 콘 텐 츠를 사용 하여 불법 웹사이트를 찾 거나 작성자
일치를 발견하면, 가장 중요 한 질문들이 aren't:
그것은 있어?
그들은:
- 그것을 사용하는 누구 일까요?
- 나타나는 다른 어디에 있니?
- 그것은 여전히 퍼지?
그 질문들에 대답하는 것은 무엇을 보호 할 수 있는 콘 텐 츠, 제거, 요청하고 예방 오용 반복 합니다.
이 곳은 역방향 검색 보호 도구 가 된-그냥 조회 가 아니다.
당신은 누출을 확인 한 후에 무엇을 해야 할
개인 사진은 온라인 포르노 사항을 확인 하거나 할 경우:
- 저장 증거 (url, 타임 스탬프, 스크린 샷)
- 업로 더한테 직접 연락을 피하기 위해
- 적절 한 제거 또는 전송 중단 요청 제출
- 계속 모니터링 reposts
유출은 드물게 일회성 이벤트다.
그들은 프로세스-그들을 막고 후속을 필요로 한다.
포르노 & 개인 사진 유출 FAQ:역 이미지 검색
내 가 어떻게 내 개인 는지 확인이나 포르노 사진을 온라인에 유출 됐습니까?
가장 신뢰 할 수 있는 방법은 역 이미지 검색을 이용 해서 원래 이미지와 여러 플랫폼 무단 재사용을 확인하십시오.
역 이미지 검색 유출 된 누드 사진 또는 명시적을 찾을 수 있어?
그래.공공 웹사이트, 포럼에서 감지 할 수 있 맨리 란 이미 지를, 및 계정, 특히 허락 없이 같은 사진이 재사용 할 때다.
누군가가 내 비공개 사진을 동의 없이 공유했는지 어떻게 알 수 있나요?
표시에는 다른 사용자 이름, 낯선 사이트에서 이미지를 찾거나 공개적으로 공유하지 않은 사진을 낯선 사람이 참조하는 것이 포함됩니다.
유출된 포르노 사진은 보통 어디에 게시되나요?
음란물 수집 사이트, 사칭 계정, 개인 포럼, 번들 다운로드 페이지 등에서 흔히 찾아볼 수 있다.
다른 웹사이트에서 내 포르노 사진을 찾으면 어떻게 해야 합니까?
증거를 먼저 문서화한 후 제거 또는 테이크다운 요청을 제출합니다.더 확산될 수 있으므로 업로더와 직접 대면하지 않도록 합니다.
역이미지 검색만으로 음란물 유출을 영구적으로 막을 수 있을까?
첫 단계야.유출을 막으려면 보통 리포스트와 재사용 콘텐츠를 잡기 위한 지속적인 모니터링과 사후관리가 필요하다.
유출된 OnlyFans 콘텐츠를 보호하기 위해 Erasa, Rulta, Enforcity 등의 가격, 성공률 & 속도를 비교합니다.무료 템플릿 & 인사이더 팁.
ERASA의 간소화된 DMCA 도구로 X (트위터)에서 성인 지향 콘텐츠를 보호하는 방법을 알아보십시오.단계별 가이드 + 무료 템플릿입니다.
실제로 작동하는 입증된 DMCA 테이크다운 단계를 사용하여 유출된 OnlyFans 사진 및 비디오를 웹사이트, 검색 결과 및 소셜 플랫폼에서 제거하는 방법을 알아보십시오.
데이팅 앱의 캐팅이나 가짜 신분증이 걱정되나요?사진과 얼굴 검색 기술을 이용해 사칭이 사기로 변하기 전에 알아낸다.
리버스 이미지 검색을 사용하여 온라인에서 사진이 나타나는 위치를 확인합니다.공개 웹 사이트 및 소셜 플랫폼 전반에 걸쳐 재게시되거나 도난당한 이미지를 탐지합니다.
