用最好的DMCA删除服务保护您的OnlyFans内容免受泄漏。快速,可靠,匿名-今天保护您的收入。
使用反向图像搜索检查你的色情照片是否泄露
目录
检查你的色情或私人照片是否被泄露,并找出它们被重用的地方。
当你开始担心你的色情或私人照片可能在网上流传时,最难的部分不是确认——而是不知道它们最后在哪里,或者它们传播了多远。
也许这些照片是和约会对象分享的。
也许你是一个创造者,你的付费内容突然对陌生人来说太熟悉了。
无论哪种方式,关注点都是一样的:我的图片已经在那里了吗?如果是的话,谁在使用它们,在哪里?
反向图像搜索通常是第一步。
但如果你想要真正的答案,就必须有目的性,而不是猜测。
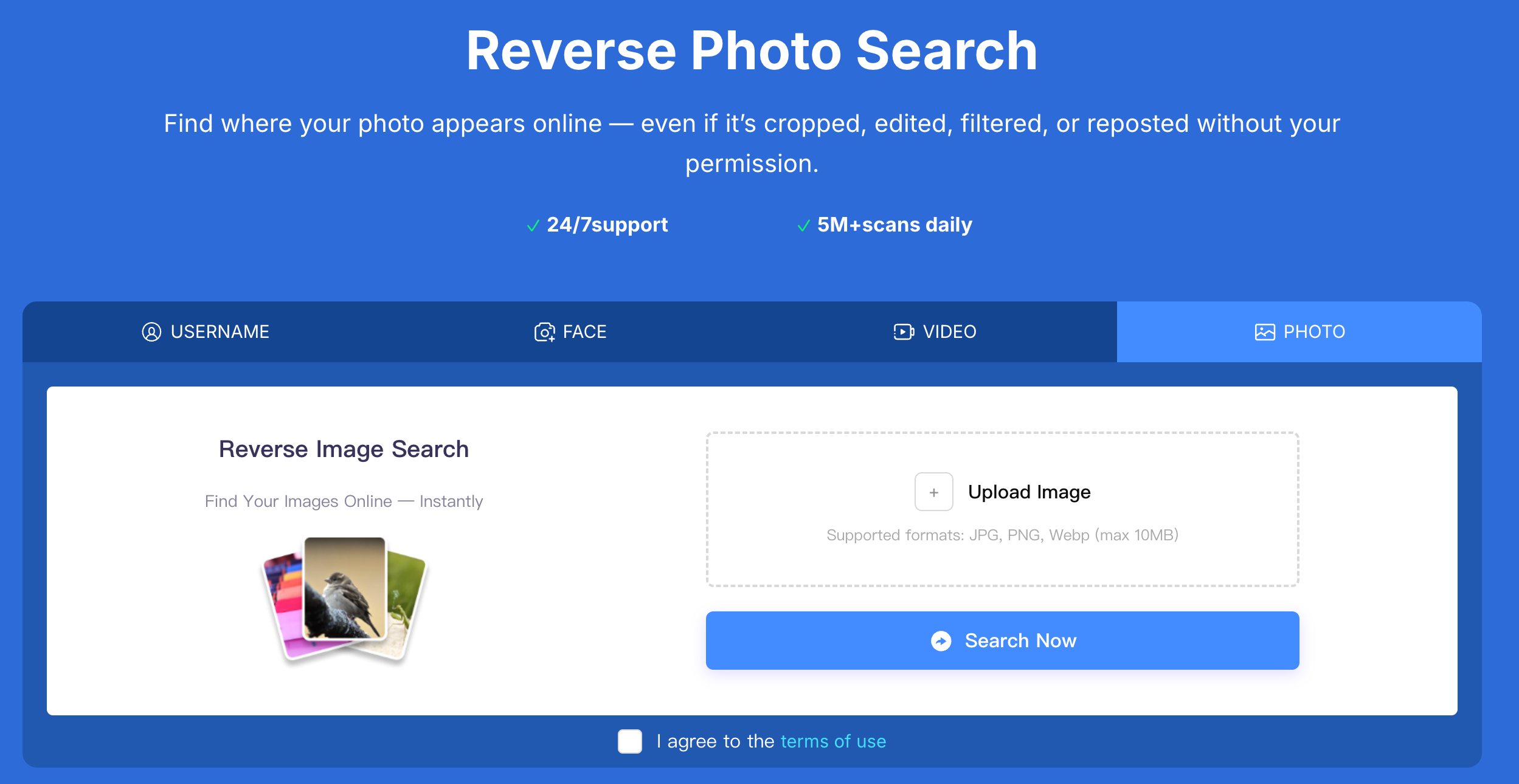
✅检查你的私人照片是否泄露使用反图像搜索在Erasa
如何积极跟踪色情或私人照片泄露
大多数人将反向图像搜索视为一次性检查:
上传一张图片,浏览一些结果,然后期待最好的结果。
这种方法几乎总是忽略正在发生的滥用。
泄漏不会停留在一个地方。
它们以不同的身份被重新发布、重命名、捆绑、出售和重用。
这就是为什么人们处理真正的泄密——尤其是创造者——依赖像Erasa这样的结构化反向搜索系统 .
不是“浏览结果”,而是 跟踪他们的原创内容在未经许可的情况下被使用的地点和方式。
区别很简单:
一种方法是寻找匹配;
另一个是寻找 滥用模式。
两个真实世界的场景,色情泄漏通常开始
一段私人关系结束后
这是最常见的诱因之一。
照片是私下分享的。
它们从未打算公开。
然后感觉有些不对劲——不熟悉的信息,复制的图片,或者你不认识的账户。
在这些情况下,泄漏通常是:
- 一开始很安静
- 在小圈子里分享
- 逐渐转发到公共网站
当大多数人查看时,图像已经移动了。
当付费成人内容被重新发布或转售
对于创作者来说,泄漏很少看起来像一个被盗的帖子。
相反,内容可能是:
- 重新上载到色情聚合网站
- 重新打包成“集合”或捆绑包
- 用于运行模拟帐户
- 以不同用户名转售
图像保持不变-上下文变化。
泄露的色情或私人照片通常会在哪里结束
根据真实的跟踪模式,泄露的图像最常出现在:
- 成人内容聚合网站建立的搜索流量
- 使用相同照片的模拟或镜像帐户
- 灰色市场论坛和私人社区
- 可下载的“内容包”以文件形式出售
- 跨平台转发网络
其中很多地方都不是你通常会去的地方——这就是为什么泄漏经常被忽视这么长时间的原因。如何进行反向图像搜索(如果你真的想要答案)
使用你所担心的形象
避免裁剪、模糊或编辑版本。
泄漏通常涉及调整大小或去除水印-原始图像给你最强的信号。
不要依赖单一的搜索引擎
不同的平台索引互联网的不同部分。
在一个地方什么都没有发现并不意味着这张照片没有在其他地方传播。
超越图像本身
照片会被重复使用——但也一样:
- 脸
- 用户名
- 发布模式
有效的跟踪将这些信号连接起来,而不是将每个图像视为一个孤立的案例。
查找非法使用你的原创色情内容的网站或创作者
一旦你找到了匹配对象,最重要的问题不是:
它在那里吗?
他们是:
- 谁在使用它?
- 它还会出现在哪里?
- 它还在蔓延吗?
回答这些问题可以让你保护你的内容,请求删除,并防止重复滥用。
这就是反向搜索成为一种保护工具的地方——而不仅仅是查找。
确认泄漏后该怎么做
如果你确认你的色情或私人照片在网上:
- 保存证据(url,时间戳,屏幕截图)
- 避免直接联系上传者
- 提交适当的移除或下架请求
- 继续监视转发
泄漏很少是一次性事件。
它们是过程——阻止它们需要后续行动。
常见问题:反向图像搜索色情和私人照片泄漏
如何检查我的私人照片或色情照片是否在网上泄露?
最可靠的方法是对原始图像进行反向搜索,并检查多个平台是否存在未经授权的重用。
反向图片搜索能找到泄露的裸照或露骨照片吗?
是。它可以检测在公共网站、论坛和账户上转发的图片,特别是在未经许可的情况下重复使用同一张照片。
我怎么知道有人未经同意就分享了我的私人照片?
迹象包括发现你的照片在不同的用户名下,在不熟悉的网站上,或者被陌生人联系,引用你从未公开分享过的照片。
被泄露的色情照片通常被贴在哪里?
它们通常出现在色情聚合站点、模拟帐户、私人论坛和捆绑下载页面上。
如果我在其他网站上发现我的色情照片,我该怎么办?
首先记录证据,然后提交删除或删除请求。避免直接面对上传者,因为它可能会导致进一步传播。
反向图像搜索是否足以永久阻止色情信息泄露?
这是第一步。阻止泄漏通常需要持续监控和跟踪,以捕获转发和重用的内容。
比较Erasa, Rulta, Enforcity等的定价,成功率和速度,以保护泄露的OnlyFans内容。免费模板和内幕提示。
了解如何保护您的成人为导向的内容在X(推特)与ERASA的流线型DMCA工具。一步一步的指南+免费模板。
学习如何从网站、搜索结果和社交平台上删除泄露的OnlyFans照片和视频——使用行之有效的DMCA删除步骤。
担心在约会软件上钓鱼或伪造身份?使用照片和面部搜索技术,在伪装变成骗局之前发现它。
使用反向图像搜索检查您的照片在网上出现的位置。检测在公共网站和社交平台上转发或被盗的图像。
